 |
| Binary Cookies |
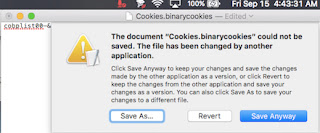
BinaryCookies is a file (sometimes) found in the Library/Cookies folder. Research indicates breach occurred in Nashville. Traffic for an AI-created website (with direct help from live hackers), or network of sites, was routed through Chicago using IP address 151.101.44.249 (in one recorded instance), registered through Fastly (based in Illinois). Firefox overlaying Safari from a Linux/Android device using a Windows Server, installed clandestinely on this workstation or another on the network, appears to have been employed in this operation, though this may also simply be record of a chain of intrusions (possibly by more than one intruder) using various devices. This event occurred prior to "TigerX Migration Successful" being found in at least one file, possibly accomplished through _launchservicesd (hidden user).
Original intrusion may have originated out of Fort Worth, TX on July 12-13, 2017. A Charter Communications account, registered under the name of a contractor who may or may not be aware of the incident, was opened at an empty, residential home (for sale) on this date. Most, if not all, affected files connected to the Equifax breach (found so far) have a July 12 or 13 timestamp.
An HSTS.plist file similar to the following (in part) was also present in Library/Cookies directory:
¯Wwiz.biz_ www.logentries.com_ mutantmonkey.sexy_ webmail.onlime.ch]itriskltd.com_ passwordbox.com_ no.search.yahoo.com_ www.capitainetrain.com_ hostinginnederland.nlYsouyar.usZairbnb.comZedmodo.com_ inertianetworks.comZsimple.com_ passport.yandex.by^koordinate.netYjelmer.uk_ tv.search.yahoo.com^www.python.org_ braintreegateway.com_ webmail.mayfirst.org_ gm.search.yahoo.comYsouyar.de_ forum.linode.comYbetnet.fr_ sandbox.mydigipass.comYcrypto.isYbaruch.me_ markusueberallassetmanagement.deZstripe.com\api.xero.com]bitbucket.org^torproject.org_ de.search.yahoo.com_ blog.cyveillance.comYgmail.com_ www.apollo-auto.comZtoner24.pl_ www.heliosnet.com_ www.irccloud.com_ isitchristmas.com_ business.lookout.com_ fj.search.yahoo.com]loenshotel.de_ www.opsmate.com_ guthabenkarten-billiger.de_ li.search.yahoo.com_ wf-pentest.appspot.com_ gemeinfreie-lieder.de_ sprueche-zur-hochzeit.deXzoo24.de_ pk.search.yahoo.com_ kleidertauschpartys.de[secuvera.de_ strongest-privacy.comYwepay.com]detectify.comZkitsta.comWnpw.net_ www.makeyourlaws.orgYromab.com_ cryptopartyatx.org\www.aclu.org_ www.therapynotes.com[twitter.com[epoxate.com_ jonas-keidel.de_ ssl.google-analytics.com\kardize24.plYimouto.my^www.roddis.net_ mt.search.yahoo.comVs-c.se_ forewordreviews.comZcybozu.comZsquare.com_ login.corp.google.comZjottit.comWbaer.im_ kinderbuecher-kostenlos.de^www.paypal.comYqetesh.de\ottospora.nl_ groups.google.com_ musicgamegalaxy.de_ fr.search.yahoo.comZanycoin.me_ therapynotes.com\certible.com_ history.google.com^it-schwerin.de_ matteomarescotti.name_ piratenlogin.de]m.gparent.orgXtonex.nlVsol.io_ docs.python.org[wildbee.org[lockify.com_ !webfilings-mirror-hrd.appspot.com_ accounts.google.com_ gl.search.yahoo.comXhaste.ch_ get.zenpayroll.com_ check.torproject.org\seifried.org_ mountainroseherbs.com_ passport.yandex.com.tr[jackyyf.comWtent.io_ mail.google.com_ www.intercom.io_ luneta.nearbuysystems.com\konklone.com_ www.zenpayroll.com\squareup.com_ espanol.search.yahoo.com_ fi.search.yahoo.com_ login.persona.org_ goto.google.com_ calyxinstitute.org_ hausverbrauch.de_ paste.linode.comWheha.co_ blog.linode.com^boxcryptor.com_ id.atlassian.com]eurotramp.com[cloudup.com_ pressfreedomfoundation.org_ winhistory-forum.net_ appseccalifornia.org_ sprueche-zum-valentinstag.de_ chromiumcodereview.appspot.comWkura.io_ ro.search.yahoo.com_ ca.search.yahoo.comYderhil.de_ passport.yandex.uaYespra.com_ openshift.redhat.com]simbolo.co.uk]keeperapp.com]addvocate.com[go.xero.comZmedium.com[gmantra.org_ ferienhaus-polchow-ruegen.de\simpletax.ca_ cr.search.yahoo.com\ethitter.com_ au.search.yahoo.com^getlantern.org]janoberst.com^studydrive.net\bl4ckb0x.com_ webmail.gigahost.dk_ rapidresearch.meZriseup.net_ ecosystem.atlassian.net_ silentcircle.com]www.wepay.com^iop.intuit.com\siammedia.co]browserid.org]bitfactory.ws^mondwandler.de_ raiseyourflag.com_ mobile.usaa.comYnexth.net_ publications.qld.gov.au_ apn-einstellungen.de_ blocksatz-medien.de_ market.android.comZwhonix.org_ projektzentrisch.de\freeshell.de_ lifeguard.aecom.com_ pa.search.yahoo.comZzotero.org_ ssl.panoramio.comYjitsi.org_ hn.search.yahoo.com_ apis.google.com^mail.yahoo.com]dl.google.com\schwarzer.it_ payroll.xero.com_ pr.search.yahoo.comZtoner24.nl[sherbers.de_ maktoob.search.yahoo.com_ reserve-online.netZscrambl.is_ rw.search.yahoo.comWmail.deYfactor.cc_ pay.gigahost.dkYpalava.tv_ qc.search.yahoo.com_ www.lookout.com\bl4ckb0x.org[f-droid.org]blacklane.com_ webfilings-eu.appspot.com_ idmsa.apple.com_ ng-
Cookies generated through a variety of methods, mostly including GoogleAPIs, further redirect URL traffic and make changes to the user's surfing experience. The most dramatic attack occurred after visiting the TigerSwan site, a domestic (and Federally-funded) terrorist group used by oil companies during the Standing Rock pipeline protest.
Some sources have tied the Equifax Breach to a CIA base in the UK. Operatives may have then used proceeds to invest in Canadian energy stocks after funneling the money through a number of world banks to BitCoin. While the latter is demonstrable through such files as that above, the former has not been confirmed by this author (at this time).
No US authorities, at any level, have contacted me regarding the Equifax breach, Sakula outbreak throughout the South (North America), or any other issues being discussed. All evidence indicates the Equifax breach, and similar criminal activity, is being conducted by actors with Federal clearance and access -- actors such as (and including) TigerSwan and similar mercenary groups -- known as "Federal Defense Contractors" working in "Extra-Judicious" (above, or outside of, the constraints of Law) capacity. The actors responsible for the Equifax Breach will have military backgrounds, and may be active service members, with direct ties to government organizations at the State and Federal level.
At least one major, paramilitary contractor is operating in and around the Decatur County, TN area. This "Neo-Confederate hate group" (a cover, or "front") appears to have direct ties to either the DOD or DHS, and may be receiving funding from these branches of the US government that often outsource their domestic terrorist efforts, known colloquially as "gangstalking."
Sakula malware is known to be a preferred methodology of the US government.
© Copyright 2017, The Cyberculturalist

No comments:
Post a Comment